Understanding mint stealer and key takeaways
For those in the security field, keeping up with the latest attack vectors is routine. Recently, an article on a newly designed information stealer caught my attention. It wasn't the first time I've come across such threats, nor was it the most alarming, but it did occupy my thoughts for quite some time into the night.
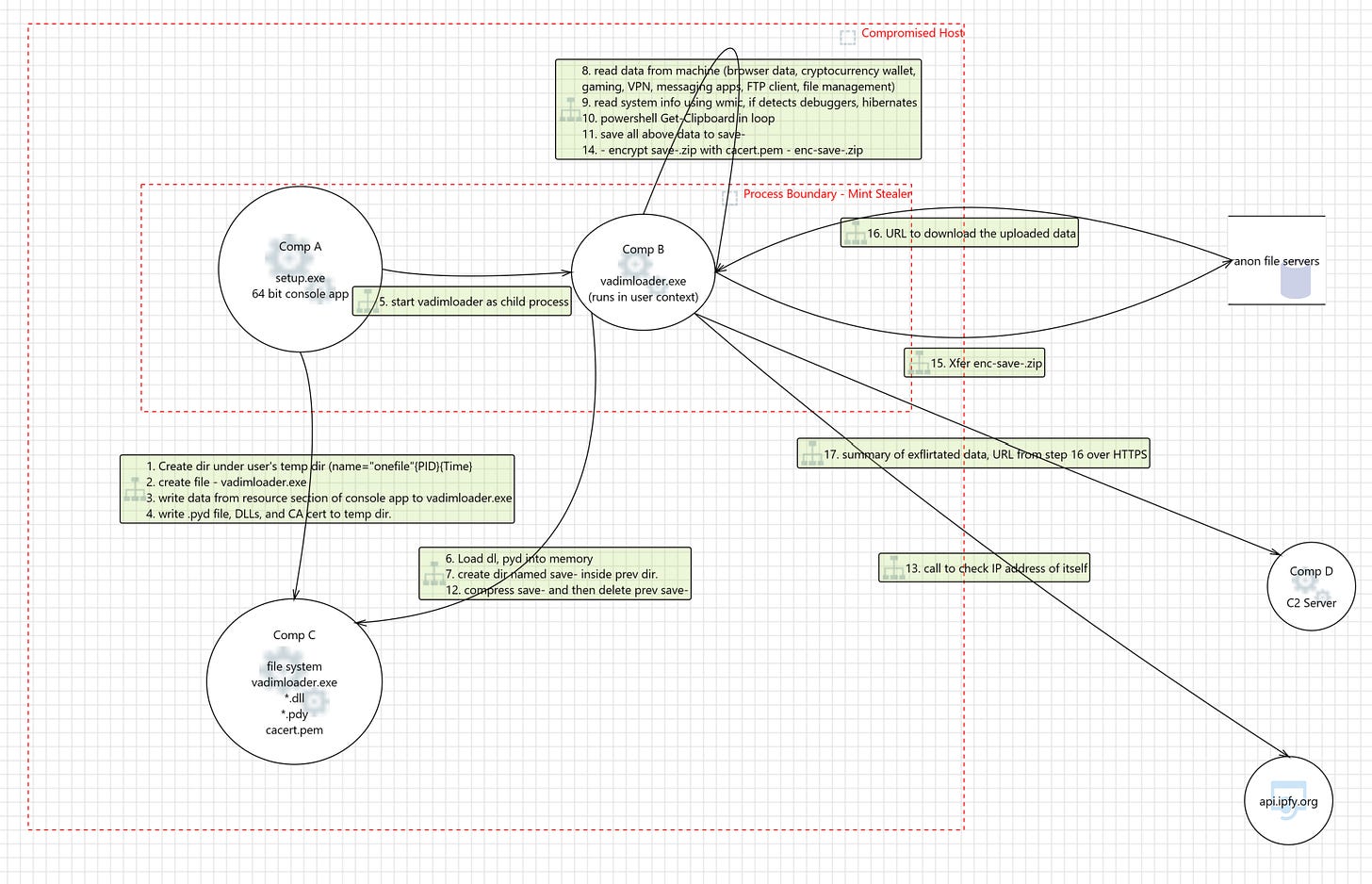
I'll tell you what kept me awake at night. To grasp its real-time operation, I developed a Data Flow Diagram for it. Take a moment and go through this.
This isn't just some arbitrary code created by an individual in isolation; it's a thoughtfully crafted software that appears to have undergone threat modeling prior to its release.
Let’s look closely at various components:
1) Component A - This is a block of code authored in C/C++, which conceals the software's additional functionality by embedding it within its resource section. Suggests – crafted by an individual with expertise in C/C++ and compilation methods.
2) Component C – Incorporates Python script, necessary DLLs, and a certificate. Indicates – created by someone acquainted with both Python and elementary cryptography, with capabilities for utilizing system calls.
3) Component B – Operates in user mode, aiming to extract data from internet browsers, e-wallets, VPN applications, and other critical assets situated in user mode. It actively monitors clipboard content and scans for any debugging tools on the system. It condenses and encrypts the gathered data before exfiltration. Implies – an intricately planned construction to elude detection while harvesting valuable data solely from user mode. It takes care not to expose the pilfered information.
4) Component D – The command and control (C2) server, identified as being utilized solely to gather details about the data siphoned off. Despite this, it boasts a flexible architecture. The C2 server retains the potential to dispatch further instructions to setup.exe for additional disruptions.
In summary, it appears this group possesses expertise in C, C++, and Python, with a firm grasp of system calls and cryptography, which makes for a strong security-related skill set.
Moreover, this software is widely supported, available for purchase on various websites and offers after-sales support through a dedicated Telegram channel.
Security engineers are faced with a new environment in this landscape. As defenders labor to secure adequate investment in product security, it appears that attackers are operating with superior resources.
Here are some key takeaways and action items we defenders can do:
1) Ensure that all your software undergoes application security checks, including threat modelling, secure coding practices, and deployment security.
2) Update and run the most current malware detection tools on all hosts.
3) Implement network monitoring to identify any unusual network behaviors.
4) Leaders in security need to be more organized as our opponents are doing.
5) Keep upskilling, the only way to survive each new day.